In this article, we’ll be checking out the top-notch VPN protocols, taking into account important factors like security, speed, and compatibility with our Aussie ISPs.
Key Takeaways
- VPN protocols are essential for securing internet connections.
- Popular VPN protocols include OpenVPN, SSTP, PPTP, L2TP/IPSec, IKEv2, WireGuard, and SoftEther.
- Consider factors like encryption strength, speed, device compatibility, and the ability to bypass geo-restrictions.
- Use OpenVPN for solid security, SoftEther for versatility and SSTP for a highly secure and encrypted connection.
- L2TP/IPSec is used for moderate security, IKEv2 for a balanced performance, and WireGuard for excellent performance.
Understanding VPN Protocols
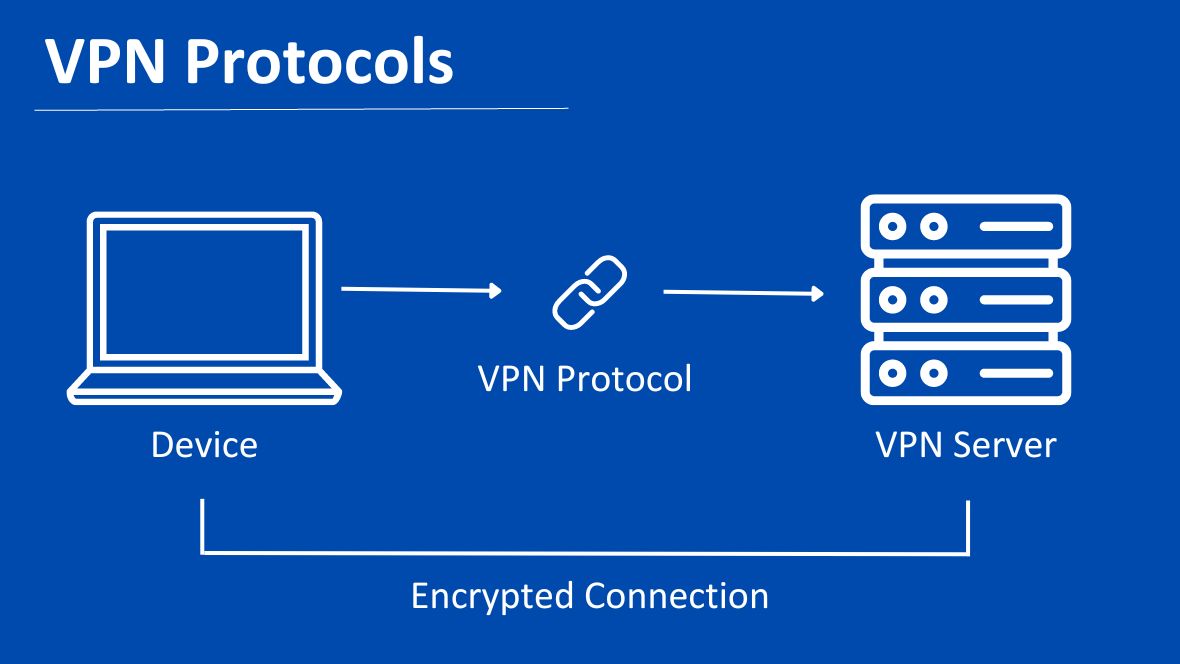
Let’s take a look at the VPN protocols and how they keep your internet connections secure. Picture this: you’re cruising through the digital world, browsing, streaming, and doing your thing. But lurking in the shadows are those sneaky hackers and data snoops, ready to pounce on your precious information. That’s where VPN protocols come to the rescue!
These clever little protocols establish a secure tunnel between your device and the websites you visit. They encrypt your data, making it all jumbled up and unreadable to anyone trying to snoop around. It’s like putting your digital secrets in a vault, only accessible to you and no one else.

So, next time you’re online, remember that VPN protocols are your digital bodyguards, working tirelessly to keep your internet connections safe and sound.
VPN Protocols for Australia
When it comes to choosing the best VPN protocols for Australia, it’s important to evaluate them in the context of the Australian market. We’ll compare these protocols based on their performance in terms of security, speed, and compatibility with Australian ISPs. Let’s delve into a detailed analysis of each protocol’s strengths and weaknesses in the Australian landscape.
OpenVPN (UDP/TCP) Protocol
Ideal for: Security-focused and widely supported
OpenVPN is a versatile and widely used VPN protocol in Australia that operates over both UDP and TCP. OpenVPN offers a robust and flexible solution for various applications and platforms.
OpenVPN supports both UDP and TCP, allowing users to choose the appropriate protocol based on their specific needs. Additionally, NordVPN is the best VPN with OpenVPN protocol in Australia. You can also try ExpressVPN and Surfshark VPN.

Pros of OpenVPN Protocol
- Strong encryption protocols.
- Supports both TCP and UDP protocols.
- Works seamlessly on various operating systems.
- Transparent and auditable.
- Accommodates large number of concurrent connections.
Cons of OpenVPN Protocol
- Setting up requires technical expertise.
- Slower speeds.
- Issues with traversing firewalls or NAT devices.
- Server quality and distance affects performance.
L2TP/IPSec Protocol
Known for: Legacy protocol with moderate security and compatibility
L2TP/IPSec is a legacy protocol that has managed to stick around despite its moderate security and compatibility.
It aims to provide a secure and private connection between remote users and their corporate networks or the internet. It’s often used in Australia for VPN configurations because it works like it is directly connected to the private network. You can use L2TP/IPSec protocol with ExpressVPN, Surfshark and NordVPN.
Pros of L2TP/IPSec Protocol
- Decent security.
- Widespread compatibility.
- Secure and private connections.
- Supported by major operating systems.
- Well-established and widely used.
Cons of L2TP/IPSec Protocol
- Not the most secure protocol available.
- Susceptible to certain vulnerabilities.
- Slower compared to other VPN protocols.

IKEv2 Protocol
Best for: Balance between security and speed, suitable for mobile devices
IKEv2 (Internet Key Exchange version 2) is known in Australia for striking a balance between security and speed, it’s particularly suited for mobile devices. It is a VPN protocol that prioritises both security and efficiency.
It offers robust encryption and authentication mechanisms, ensuring a secure connection. Moreover, IKEv2 is designed to handle network changes seamlessly, making it ideal for mobile devices that frequently switch between Wi-Fi and cellular networks.
Pros of IKEv2 Protocol
- Strong security.
- Quick reconnections.
- Optimised for mobile devices.
- Good performance and faster speeds.
- Battery-friendly.
Cons of IKEv2 Protocol
- Limited compatibility.
- Relatively complex setup process.
- Issues with certain firewalls.
- Limited support from VPN providers.
- Not as auditable as open-source protocols.
WireGuard Protocol
Preferred for: Latest protocol with excellent performance and simplicity
WireGuard VPN protocol has been gaining attention in Australia for its excellent performance and simplicity. It boasts a streamlined codebase, making it easier to audit and maintain. With its focus on simplicity, WireGuard offers a straightforward setup process and intuitive configuration options, making it more accessible to users.
Pros of WireGuard Protocol
- Excellent performance.
- Simplified setup.
- Strong security.
- Efficient codebase.
- Supports dynamic IP addresses.
Cons of WireGuard Protocol
- Limited compatibility.
- Still relatively new.
- May lack certain advanced features.

Softether Protocol
Recognised for: Versatility and flexibility in creating a secure VPN connection
Developed by SoftEther Corporation, it is an open-source VPN software that supports various VPN protocols, including SSL-VPN, L2TP/IPsec, OpenVPN, and Microsoft’s SSTP.
SoftEther protocol stands out for its ability to operate on multiple platforms, including Windows, Linux, macOS, FreeBSD, and Solaris. It also offers features like high throughput, low latency, and dynamic multi-VPN connections.
Pros of Softether Protocol
- Versatile and flexible.
- Cross-platform compatibility.
- High throughput and low latency.
- VPN over HTTPS bypasses firewalls.
- Dynamic multi-VPN connections.
Cons of Softether Protocol
- Setup complexity for beginners.
- Limited mainstream adoption.
- Limited official support channels.
SSTP Protocol
Known for: Providing a highly secure and encrypted connection
The SSTP (Secure Socket Tunneling Protocol) is widely recognised for its role in providing secure and encrypted VPN (Virtual Private Network) connections. It offers robust security measures, utilising SSL/TLS protocols to ensure data confidentiality and integrity during transmission. SSTP is particularly favoured for its compatibility with Windows operating systems, where it is natively supported.
Pros of SSTP Protocol
- Highly secure and encrypted.
- Utilises HTTPS port.
- Native support in Windows OS.
- Excellent performance.
- Seamless integration with Windows-based networks.
Cons of SSTP Protocol
- Limited compatibility with non-Windows OS.
- Concerns about privacy.
- Not as flexible as open-source protocols.

Tips for Choosing and Setting Up a VPN Protocol in Australia
1. Researching and Selecting a Reputable VPN Provider
When it comes to VPNs, quality and reputation are paramount. Before selecting a VPN provider, do thorough research to understand the credibility and reliability of the service. Look out for VPN services with a strong track record for privacy, security, and speed.

2. Considering the Server Network and Locations
The effectiveness of a VPN heavily depends on the network and the location of its servers. The more geographically spread out the servers, the better the chances of a strong and stable connection, and the more choices you’ll have for bypassing geo-restrictions.
3. Ensuring Compatibility with Devices and Operating Systems
Before settling on a VPN, you need to ensure it’s compatible with the devices and operating systems you use. The majority of VPNs will support the most common platforms, including Windows, macOS, iOS, and Android. However, if you’re using less common platforms like Linux or certain smart TVs, you’ll want to verify that the VPN supports these as well.
4. Setting up and Configuring the Chosen VPN Protocol
Setting up a VPN generally involves installing the provider’s application on your device. However, the configuration process can vary depending on the VPN protocol you choose. The protocol determines how your data is routed and secured over the network. Common choices include OpenVPN, IKEv2, and WireGuard, each with its own strengths.
5. Testing the VPN Connection for Security and Speed
After you’ve set up your VPN, it’s crucial to test it. You want to ensure that the VPN is both secure and fast enough for your needs. For security, you can use online tools like DNSLeakTest.com and Speedtest.net for speed.
Potential Challenges and Workarounds
Let’s take a closer look at some potential challenges you might face when using a VPN in Australia, and how to work your way around them.
1. Dealing with VPN Blocks and Restrictions Imposed by Australian ISPs
Some Aussie ISPs might have VPN blocks or restrictions in place, making it harder for you to use your chosen VPN service. These blocks can be a real hassle, but there are a couple of workarounds you can consider.
Firstly, try switching your VPN’s protocol. If that doesn’t work, consider using a VPN with stealth or obfuscation technology.
2. Overcoming Potential Slowdowns in Internet Speed
A VPN will usually slow down your internet speed a bit, mainly due to the encryption process it uses to secure your data. However, if the slowdown is too severe, there are a few tricks you can try.
First, you might want to try connecting to a different server. If you’re still struggling with slow speeds, it might be worth checking with your VPN provider’s customer support.
3. Addressing Concerns About Logging and Data Retention Laws in Australia
By law, Aussie telecom companies must retain certain types of data for two years, which can include details of your online activities. To avoid this, you might want to consider using a VPN provider based outside Australia, particularly in a country with strong privacy laws. Look for a provider with a strict no-logs policy.
Which VPN Protocol should I Use in Australia?
Let’s go over some of the best VPN protocols suitable for use in Australia, taking into account the needs of different activities such as streaming, torrenting, online gaming, and business use.
Table 1. VPN Protocol Recommendations Based on Different Use Cases in Australia
| VPN Protocol | Best For | Pros | Cons |
| OpenVPN | Streaming, torrenting | High security, open-source, balance of speed and security | Can be complex to set up |
| WireGuard | Online gaming, streaming | Fast, simple, modern cryptography | Not supported by all devices/services |
| IKEv2/IPSec | Mobile use, business use | Stable, secure, good for re-establishing lost connections | Might not be the fastest |
| L2TP/IPSec | General browsing | Secure, reliable, widely supported | Not the fastest protocol |
| PPTP | Speed-focused activities (where security is not a concern) | Fast, easy to set up | Less secure |
| SoftEther | Streaming, torrenting, business use | High speed, secure, versatile, can bypass network restrictions | Not widely supported by VPN providers |
Final Thoughts
Choosing a VPN protocol in Australia involves balancing speed, security, and compatibility. Popular protocols like OpenVPN, WireGuard, and SoftEther offer unique benefits. The right choice depends on your specific needs and the capabilities of your VPN provider. Keep in mind the server network, data logging policies, and potential VPN blocks. As the digital landscape constantly evolves, staying informed about VPN trends will help ensure an optimal, secure internet experience. Remember, the best VPN protocol today might not remain the best tomorrow, so continual reassessment is beneficial.
Frequently Asked Questions
Which VPN Protocol Delivers the Fastest Speed in Australia?
When it comes to sheer speed, the Point-to-Point Tunneling Protocol (PPTP) often stands out as the fastest VPN protocol in Australia. It is typically used when speed is a higher priority than security, such as when streaming geo-restricted content.
What is the Most Prevalent VPN Protocol Utilised?
OpenVPN, a highly popular VPN protocol, is favoured due to its balance between speed, dependability, and robust security measures. As an open-source solution, OpenVPN benefits from continuous scrutiny and improvements made by the global cybersecurity community.
Is L2TP or IPSec Superior in Terms of Performance and Security?
Internet Protocol Security (IPSec) often surpasses Layer 2 Tunneling Protocol (L2TP) in providing superior security and stability. IPSec offers robust encryption, making it a reliable choice for secure data transport. On its own, L2TP doesn’t offer encryption, but it’s frequently paired with IPSec to bolster its security capabilities.
Which VPN Protocol Consumes the Least Amount of Data?
The Point-to-Point Tunneling Protocol (PPTP) is known for its low data usage, making it a favourable choice for those with data constraints. However, this efficiency comes with a trade-off, as PPTP’s security measures are less robust compared to other VPN protocols.